Biometric authentication methods - Complete Guide!
Biometric data is a unique identifier of each person. Let's take a closer look at Types of biometric authentication, examples and frequently asked questions.
What is biometric authentication data
Biometric data are patterns of behavior and physical traits that can help people to be identified and verified. These types of data are unique, permanent, and collectible. When combined with other types of information, they can be used to authenticate a person's identity and unlock devices.
Some examples include facial recognition, fingerprint scanning, and iris scanning. After biometric data is collected, it is securely stored in an encrypted database. Biometric data cannot be changed or lost, unlike PINs or tokens, which can be changed by users. It is also extremely difficult to modify or alter biometric data, making biometrics an ideal choice for applications that require authentication.
The GDPR defines biometric data as "personal data that is determined by the physical, physiological and behavioral characteristics of an individual, for reasons of public interest." Many organizations are using biometrics to create more secure authentication methods, using it as part of data analysis and creative research.
BIOMETRIC AUTHENTICATION
Biometric authentication is becoming increasingly important for online security , since the 27% of Americans believe biometrics are a more secure alternative to passwords. Additionally, biometric authentication eliminates the need for people to remember multiple passwords for online activities. According to Intel Security, the average person has up to 40 different online accounts and login.
The public is ready for biometrics, especially millennials, who see biometrics as a more secure alternative to passwords.
“As such, it is a smart way to protect a person's information and prevent identity theft”
VIDEO: What is Biometrics?
Biometric Authentication Methods Classification
They are classified into 3 types and subtypes, explained:
1.Types according to their nature
They can be one or a combination of these and are:
1.1. Universal biometric data
are those found in all people without distinction. Example the height.
1.2. Unique biometrics
These are the records that are unique per person. Example fingerprints, eye iris data, etc.
1.3. Permanent
Which do not change over time.
2.Types according to their nature
Fingerprint, Facial recognition, Recognition of the iris, Geometry of the hand, Recognition of the retina, Vascular recognition.
3. Types according to their behavior and personality characteristics
Signature recognition, Handwriting recognition, Voice recognition, Keyboard writing recognition, Handwriting recognition the way of walking
Biometric Authentication Methods and Examples
1. Fingerprint
Fingerprint biometrics is generated by the image data of a user's fingerprints, swiping their fingertip over a laser reader. This image is stored in memory, to be used by a processor that compares images registered in a database.
The fingerprint biometric device contains a dedicated sensor chip and processing hardware. The sensor chip is attached to the device's host system and captures a partial image of a person's fingerprint. The results of the comparison are provided to the host system, requesting server, or other element of the overall system for approval.
Disadvantages and criticisms
Fingerprint recognition has become one of the most reliable biometric technologies. However, security experts have warned that dirty fingerprints can interfere with the scanning process. Furthermore, a Japanese researcher has shown that a gelatin-based fake finger can fool optical fingerprint scanners.
2. Facial recognition biometrics
Facial recognition technology is a growing technology that uses biometric data collected from a person's face to identify and verify them. The accuracy of facial recognition depends on the accuracy of the images obtained through CT scans taken of people's faces.
While facial recognition technology is becoming more advanced and useful, some researchers are concerned that its use could lead to discrimination and abuse. This raises concerns about privacy and racial bias.
3. Iris pattern biometry
Iris recognition is performed using an eye scanner that must first capture a pattern in the iris. A system must then match that pattern to a digital identity. Near-infrared light can capture high-quality iris images without causing the iris to shrink. "Iris biometry is a highly accurate and fast recognition method" Iris scanning is highly accurate and fast, and can even be performed on people who wear contact lenses.

See video "All about the technology of recognition by the iris of the eye".

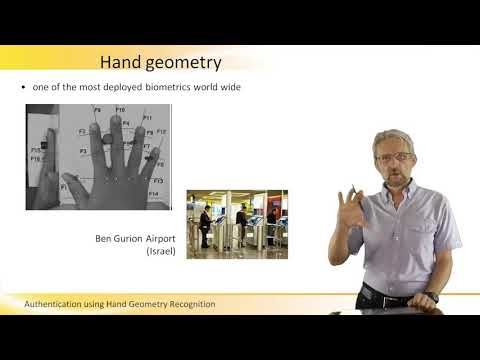
4. Hand shape biometric data
Hand geometry recognition is a form of biometric identification that uses three sequential images of a hand to determine identity of a person. The system uses an angled mirror to take images and analyzes the 40. image points. This information creates a biometric template that is unique to a person. See video: Authentication of the geometry of the hand.
5. Retinal biometric data
The first step in retinal recognition is to acquire an image of the retina. Once this is done, the image is converted to a digital format and cross-referenced with a database. The second step is to capture the pattern of blood vessels in the retina. The entire process can take up to a minute. Usually three to five images are taken for a complete match and comparison.
The retina is one of the most important biometric characteristics for identification. Its unique features make it difficult to copy. Because it is permanent, it is considered the most secure biometric to use.
However, the public has the potential to perceive retinal scanning as an intrusion into their privacy and health. Therefore, this type of recognition is mainly used in conjunction with access control systems in high-security facilities.

The advantage of retina recognition is its high precision . The error rate of this method is about one in a million
The technique requires very close contact between the subject and the scanning device. Also, it uses a beam of light that is absorbed deep into the eye. As a result, it is considered invasive. However, the iris pattern can be captured using a near infrared light source, which is much safer for the human eye.
6. Biometrics by vascular recognition
This form of identification uses a device that measures and displays the shape of the distribution of veins in an individual. The sensor is usually worn on the fingers and the wrist of the hand.


The system uses near-infrared rays to analyze blood vessels. These rays pass through the fingers or wrist of the hand and are partially reflected and partially transmitted, allowing you to identify a pattern of the veins in the hands.
In addition, vascular biometry is considered more reliable than fingerprint biometrics. Its FRR and FAR are significantly lower than fingerprints.
7. Signature Recognition

Signature biometrics uses information about physical activity of the signature Important features include the order of the stroke, the pressure applied, the movement of the pencil, the angle, and the time taken to sign. Some systems also compare the visual image of a signature.
Until now, paper signatures have been an effective way to validate the identity of the signatory. While not an exact science, signatures can be a cost-effective and reliable method of identification. For example, banks have long used signatures for verification of documents or checks. However, this verification process is still highly dependent on humans.

8- Recognition by handwriting biometrics
Biometrics by handwriting consists of recognizing patterns in a person's handwriting in order to identify it. Therefore, it is suitable for use in a variety of applications. However, you must be able to distinguish between a writer's handwriting and that of other writers.
"This is a challenging task for the computer, therefore approval from a verification expert is generally required"
It is important to note that biometric writer identification systems should not be confused with optical character recognition, which identifies the content of a text and not the author.
9. Voice biometry
It is the process of transforming what a person speaks into mauine language. It is the identification of a person's voice record by a machine, having previously converted the voice record in the language of a machine, recording it in its memory so that the machine later has the capacity to recognize the sound record. And so it can be used to verify that the person speaking is really who they say they are.
It has several advantages, such as the ability to verify identity without having to reveal information staff. Another advantage of voice biometrics is a great way to reduce biometric testing costs. This type of biometric data is cheaper to obtain and integrate into other devices.
The downside, voice biometrics is not as accurate as other biometric modalities. Also, the quality of the speech sample is affected by background noise, making it less suitable for noisy environments. The current and massive use of biometric data recognition by voice is in cell phones, in applications that allow users to open and close sessions.
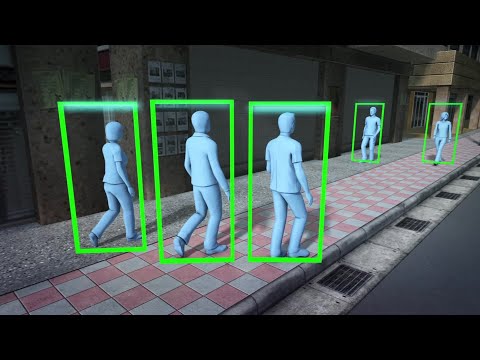
10. Gait recognition (gait buimetry)
Gait biometrics uses algorithms from video signals and sensor data to identify characteristics of an individual's gait. The resulting data is compared to a database to detect gait variations. And if these gait variations are within the permissible margins, the individual is identified. Gait
recognition software can compare a person's silhouette with a database of gait patterns. Some algorithms are based on visual information, while others use data from sensors to create a 3D model of a person's silhouette. The entire process involves data capture, silhouette segmentation, and contour detection. The system also uses machine learning to improve its performance.
Since each gear has different characteristics, each recognition algorithm has to learn from a variety of variants. This leads to a better ranking. See Video of biometrics for gait recognition:
10. Biometric recognition by the shape of the ear
It is the ability to recognize the ear helix by its contours. The recognition pipeline uses an iterative refinement process, which aims to produce the most accurate alignment between the model and the test ear. The technique uses classifications to recognize the ear helix and other structures.
The system can be used in two modes, identification and verification. In identification mode, the system verifies the identity of a subject before searching its database to find the ear of that individual. The technology was developed by a team led by Professor Mark Nixon of the University of Southampton.
Related questions:
Biometric health exams for employees. Why do them?
- Because Biometric testing can help employers improve their health, but they can also reveal a lot about your employees.
- Biometric screenings also help employers maintain a healthy workforce by improving employee performance.
- If an employee has little sleep, for example, a Biometric assessment can help them realize this and begin to change their lifestyles.
- Using biometric data, employers can identify health risks, including cholesterol, and provide the best treatment options to employees. ados.
Help develop a corporate wellness program, including screening for diabetes, cardiovascular disease, and high blood pressure, etc.
- Biometric scans are a great way to encourage employees to stay healthy.
Health insurance providers may also require biometric screenings as a condition of their policies.
See biometric examination video:
What is biometric access control?
Biometric access control is a very popular security method. Biometrics is a form of pattern recognition that uses biological characteristics to generate identification data. Biometric login data can be entered through a fingerprint (which is the most widely used), then the system compares the entered data with the stored data, allowing you to automatically open access points only to authorized ones to enter.
See also: